![KINGDOM HEARTS III Re Mind [DLC] Trailer](https://i.ytimg.com/vi/YWXio_Jra9s/maxresdefault.jpg)

![KINGDOM HEARTS III Re Mind [DLC] TGS 2019 Trailer](https://i.ytimg.com/vi/l4D_Cu9Ad0s/maxresdefault.jpg)
























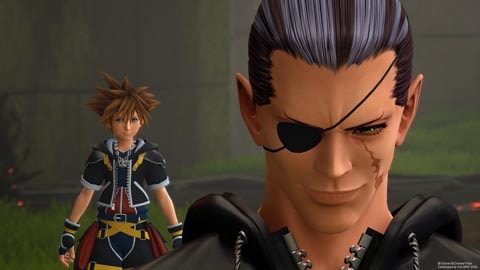
KINGDOM HEARTS III tells the story of the power of friendship as Sora and his friends embark on a perilous adventure. Set in a vast array of Disney and Pixar worlds, KINGDOM HEARTS follows the journey of Sora, a young boy and unknowing heir to a spectacular power. Sora is joined by Donald Duck and Goofy to stop an evil force known as the Heartless from invading and overtaking the universe.
Through the power of friendship, Sora, Donald and Goofy unite with iconic Disney-Pixar characters old and new to overcome tremendous challenges and persevere against the darkness threatening their worlds.
![KINGDOM HEARTS III Re Mind [DLC] Trailer](https://i.ytimg.com/vi/YWXio_Jra9s/maxresdefault.jpg)

![KINGDOM HEARTS III Re Mind [DLC] TGS 2019 Trailer](https://i.ytimg.com/vi/l4D_Cu9Ad0s/maxresdefault.jpg)






































































HWID (Hardware ID) is a unique identifier assigned to a computer's hardware components, such as the motherboard, CPU, and hard drive. It's used to identify a specific computer and can be used to lock software licenses to a particular machine. HWID spoofing involves manipulating the HWID information to make it appear as though the software is running on a different computer.
Enigma Protector HWID bypass top refers to a method of bypassing Enigma Protector's HWID protection using a HWID spoofing tool. This allows users to bypass the HWID check and run the protected software on a different computer. The "top" part of the keyword refers to the best or most effective methods of bypassing Enigma Protector's HWID protection.
Enigma Protector is a software protection system designed to protect applications from piracy, reverse engineering, and unauthorized use. It provides a range of protection features, including HWID locking, code encryption, and anti-debugging techniques. Enigma Protector is widely used by software developers to protect their applications from being cracked or tampered with.
Enigma Protector HWID bypass top is a complex topic that requires careful consideration. While bypassing Enigma Protector's HWID protection may seem like an easy way to access protected software, it's essential to understand the risks and consequences involved. Software developers use protection systems like Enigma Protector to protect their applications from piracy and unauthorized use. Instead of seeking bypass methods, users should consider purchasing legitimate software licenses or exploring alternative solutions.
